No Kings: Jokers Wild!
The guy vibe coding White House adware accused of pinging Trump donors' location every four minutes has a whole persona dedicated to wild conspiracies.

Why is it always a Friday afternoon!? I was just about to unplug for the day when I noticed a new message in the group chat. It was a link to the most recent blog post from the White House, followed by: 🤣🤣🤣🤣🤣🤣🤣🤣🤣🤣 NO.

Naturally, I had to know more. The first response was speculation about the potential for embedded trackers and exposed intents siphoning data off from unsuspecting users. Obviously, I had to find out. So, I pulled a copy of the Android mobile app and got to work. My initial reaction was confusion as to why an app I expected to be a glorified WordPress site was 90 MB.
Then, I realized it was partially because the developer chose to release it without enabling ProGuard, which is frequently used to shrink and optimize Android apps, while also making it harder for the security-curious like myself to see what's going on under the hood. This was very likely the first and last production mobile app I've ever seen that didn't employ this basic step. This was going to be good!!!
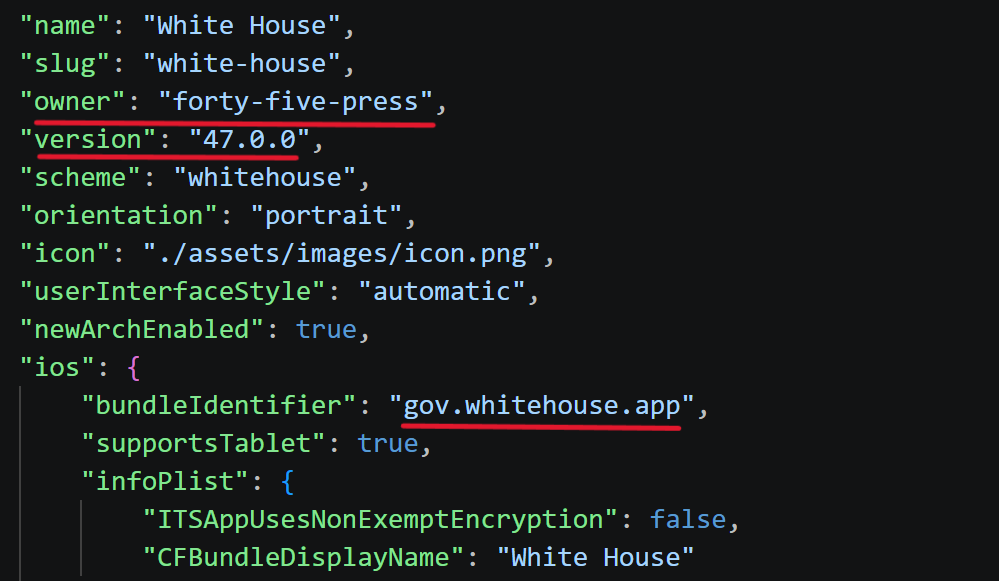
As much as it almost was, this isn't going to be a post about how I reverse engineered the new White House app. It was Friday evening, and I needed a California burrito. After identifying multiple trackers, aggressive permissions, and generally bad practices, I decided to peer into the app.config file. Much to my surprise, I was greeted with a potential developer identity: forty-five-press.
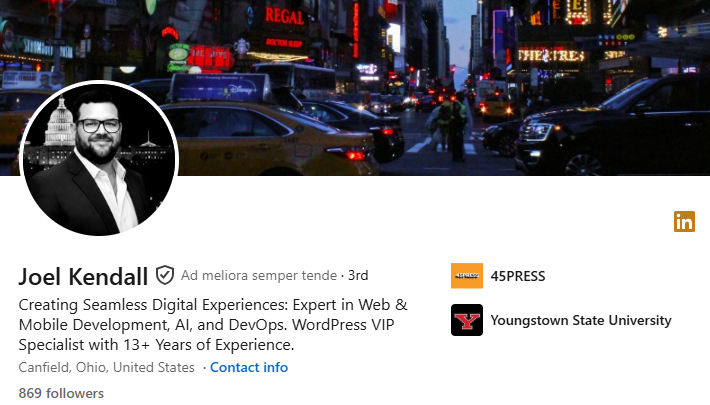
Hmm... Interesting choice. A quick Google search returned a website and a LinkedIn profile for 45PRESS, a WordPress design company in Canfield, Ohio (Pop. 7,699). Notably, 45PRESS claims to have experience designing mobile apps and lists customers such as the Senate and House of Representatives. With that little discovery, I decided to kick back with the new season of One Piece.

This morning, I decided to take a quick peek into the app's JavaScript to see if anything jumped out at me. As I began searching the internet for the WordPress strings in the React Native bundle, I came across an excellent blog post from Thereallo documenting their teardown of the app, which included many of my own observations and numerous others. I strongly encourage you to read their post for a deeper understanding of just how badly this app was done.

"An official United States government app is injecting CSS and JavaScript into third-party websites to strip away their cookie consent dialogs, GDPR banners, login gates, and paywalls."
As you may recall, Saturday was No Kings, which meant it was again time to put down the keyboard and go get civically fit through some community participation. That's enough gratuitous pics. Let's get into the good stuff!

After I returned from my leisurely stroll downtown this afternoon, I decided to do a little more research related to 45PRESS. Aside from Thereallo's blog post, I was surprised there hadn't been more coverage of the app's developer. There had to be more than just the tenuous 'same name, same type of work' connection. There was.
The fun thing about providing technology on behalf of the United States government is that people want to get paid to do it, and when those people don't already work for the government, they get paid through very public contracting mechanisms. Had 45PRESS ever been awarded one of these contracts? They had. On February 9, 2026, the Executive Office of the White House awarded over $1.4 million to 45Press, Inc., for services including support, maintenance, development, and enhancement of wh[dot]gov and all associated stand-alone sites, subsites, and microsites, which require 24/7 access.
That seems to align with when someone would have reasonably started thinking about rushing half-baked ideas off the South Portico, but contractors don't just show up and get million-dollar awards, right? Not exactly... To find where this contract was solicited, we head over to SAM.gov where it was first published on December 23rd, 2025, and due on January 6, 2026. If that seems like a huge rush over a long holiday weekend, that's because it is.
Surely, if someone is being hired to maintain the prestigious White House website, they must have a long history of working with the government, right? Well, sorta... 45Press also appears to have been awarded a contract going into the first Trump administration, but it's not clear whether funds were ever obligated. At this point, I really wanted to know who was behind this company, but I still wasn't finding any coverage of their role in the app. So, let's make some!
Let's start with 45PRESS CEO and founder, Joel Kendall. According to his LinkedIn page, Kendall founded 45PRESS in late 2013 and wears a lot of hats. He doesn't mention what color they are... Most recently, Kendall celebrated his company's receipt of WordPress Premier Partner status, which likely had a lot more to do with landing the White House contract than the previous twelve years of work where the invitation had not been extended his way.
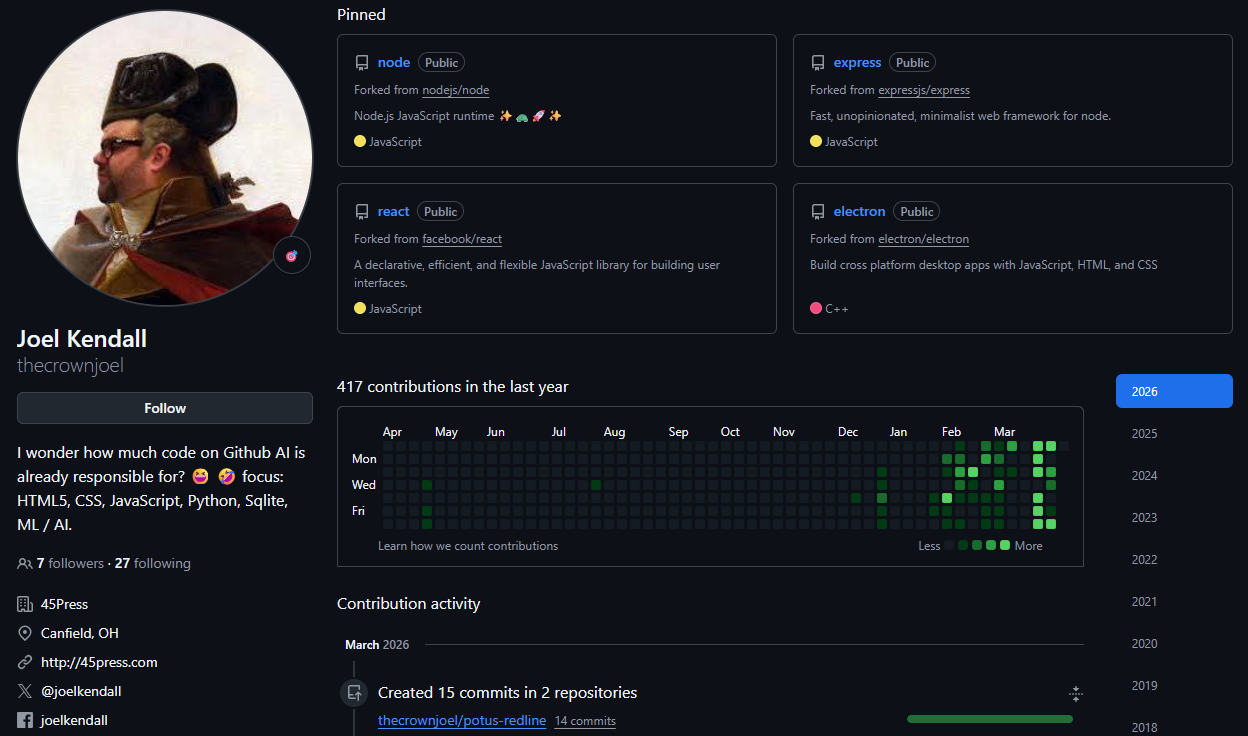
But is his code 'leet'? Well, you'll have to decide that for yourself over on his GitHub page. There are plenty of interesting places to start, but I might suggest potus-redline, which he describes as a "bot-proof, verified-citizen communication channel between the White House and the American people. Browser extension + WordPress plugin." There are also plenty of stale sports betting repos and a few other very strange ideas. Also, socials!!!
Kendall has been on Twitter since 2008, but he's not much of a talker. 45PRESS has an equally disappointing presence for a company now running the world's largest mouthpiece. Never fear! There is one passion Kendall has fervently represented for the last several years—paranormal conspiracy theories!!!

Y'all! The guy vibe coding White House adware accused of pinging Trump donors' location every four minutes has a whole persona dedicated to wild conspiracies.
Here are just a few:
Are Aliens and UFOs real? PROVE ME WRONG!
9/11 WTC controlled demolition! | FDNY
Did Nazis escape on a UFO?
1997 Terrifying Bigfoot 911 Encounter
Alright, where does that leave us? We've got a $1.4 million taxpayer-funded spyware platform leaking data like a pool house bathroom at Mar-a-Lago, vibe-coded by a tech bro whose primary expertise seems to be hunting for cryptids and unraveling 9/11 conspiracies. I know Hollywood is right down the street, but you can't make this stuff up. It's a masterclass in how not to do government tech with a paranormal conspiracy cherry on top. I think the next question that needs to be answered is how this guy ended up with enough clout to get this contract in the first place.
My money is on sports betting with Don, Jr. Any takers?
UPDATE: After publishing this a challenge arose to Thereallo's analysis of the White House app's tracking capability, which appears to be based on changes that were made between version 47.0.0 and 47.0.1 of the app. My initial analysis was based on version 47.0.0, while Thereallo appears to have been reviewing version 47.0.1. Version 47.0.0 did implement location permissions, and a location service which was reflected in decompiled Java and React Native code. Dynamic analysis was not conducted; therefore, I can't confirm that the location services functioned.
The following nine permissions were removed from the app between versions and are no longer present, which should negate most location tracking methods and some other frequently abused permissions:
android.permission.ACCESS_COARSE_LOCATION
android.permission.ACCESS_FINE_LOCATION
android.permission.READ_EXTERNAL_STORAGE
android.permission.SYSTEM_ALERT_WINDOW
android.permission.WRITE_EXTERNAL_STORAGE
android.permission.ACCESS_WIFI_STATE
android.permission.USE_BIOMETRIC
android.permission.USE_FINGERPRINT
android.permission.FOREGROUND_SERVICE
It is unclear whether the removed features were erroneously included in the original deployment, or if they were removed as a result of public scrutiny. In an article discussing the matter, the IB Times identified the app developer as Dev Forty Five, LLC, based on a Lemmy community chat. However, a query of USAspending.gov returned no results for Dev Forty Five, and no further justification was provided for this claim.
The IB Times further cited an Exodus report in an assertion that the app contained a Huawei tracker. This detection appears to be a false positive and may have been triggered by references to Huawei notification services within how the app handles notification on Huawei devices. I was unable to confirm the presence of Huawei tracking services during my review.
As with all reverse engineering tasks, mobile app analysis is a considerably complex task that often cannot definitively confirm or disprove malicious behavior. Dynamic analysis can be helpful in determining whether features are being actively used and/or abused, but it often can't provide a definitive answer. Given the removal of the offending permissions, I am unlikely to do further technical analysis of version 47.0.0 of this app, but a copy of the APK is available on request or through many APK mirror sites.
Second Update: Additional analysis by atomic.computer, including dynamic analysis of the iOS app appears to have confirmed Thereallo's findings and reflects the removal of location tracking in recent updates. Their dynamic analysis indicated that while the location tracking code is still present and could be remotely activated, it does not appear to be in use at this time.
For refence, Android mobile applications are not able to interact with Android's location services without declaring location permissions (which were removed after version 74.0.0) in the manifest and requesting user approval. However, other collected identifiers may allow the developer to infer location based on third party data suppliers.
This post has been updated to reflect the current nature of the app's location features.

